The 2026 Refurbished Phone Mandate: A Zero-Trust Protocol or a Data Breach Waiting to Happen
Meta Description: By 2026, your refurbished corporate phones will be either a hardened security asset or a critical breach vector. Implement this actionable Zero-Trust protocol to ensure data-pristine devices and transform your procurement into a strategic advantage.
Title: The 2026 Refurbished Phone Mandate: A Zero-Trust Protocol or a Data Breach Waiting to Happen
Introduction: The 2026 Procurement Crossroads
What if your IT department’s sustainability effort is the very loophole that bypasses your entire security stack? As we accelerate toward 2026, three forces are converging: punishing new data regulations, AI-driven supply chain attacks, and the non-negotiable shift to circular tech economies. The refurbished phone market is exploding, but treating it as a simple cost-saving tactic is a profound strategic error.
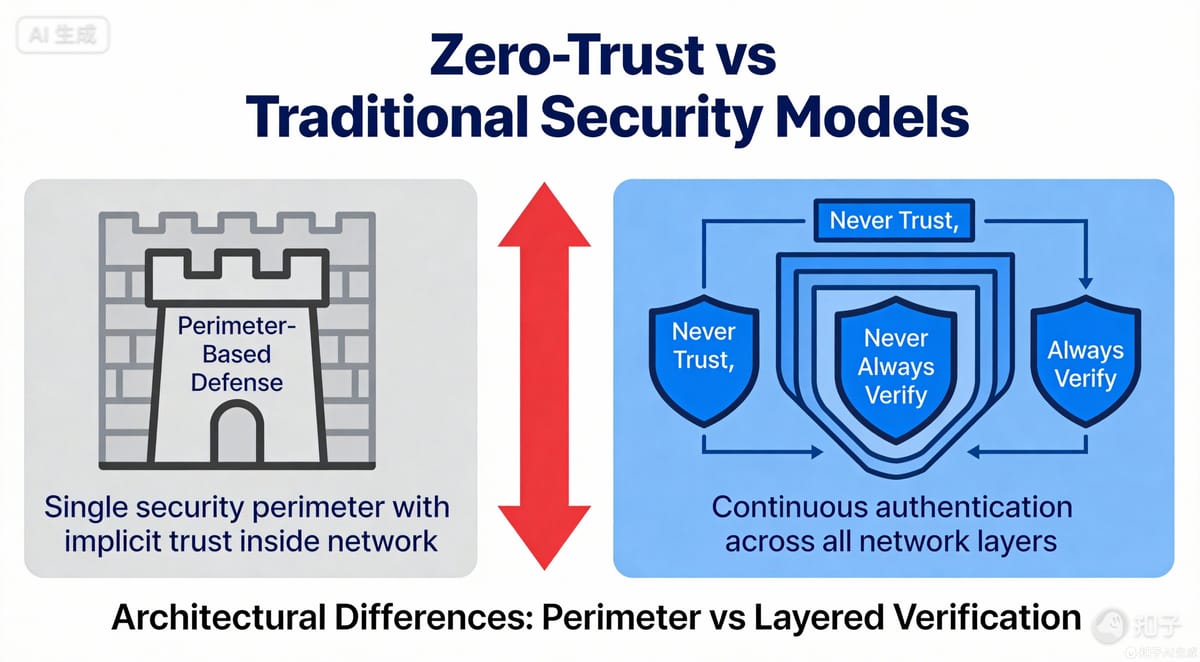
This is a foundational shift in procurement philosophy. One path leads to hidden firmware backdoors, data fragment recovery, and regulatory ruin. The other forges a resilient, sustainable, and verifiably secure mobile fleet. This guide delivers the definitive, step-by-step Zero-Trust protocol to guarantee every corporate refurbished device is data-pristine—a cryptographically verified, trusted node in your 2026 network from first boot to final decommissioning.
Beyond the Wipe: Why "Clean" is a Dangerous Illusion in 2026
The era of trusting a factory reset is over. It’s a vulnerability. Standard wipes leave recoverable data artifacts and are utterly blind to sophisticated implants residing in firmware, bootloaders, or even tampered hardware components.
The 2026 threat model for refurbished devices demands a new standard:
- Hardware-Level Compromise: Malicious or counterfeit components (modems, NFC chips) introduced during refurbishment.
- Firmware Persistence: Rootkits that survive OS reinstallation, lying dormant until activated.
- Opaque Provenance: A murky chain-of-custody where a device could have been compromised at any stop.
This is why we must move to the "Data-Pristine" Standard: A device where both hardware integrity and software state are cryptographically verified against a known-trusted baseline, seamlessly integrating into your corporate Zero-Trust architecture.
Pillar 1: The 2026 Sourcing & Vetting Protocol – Building Trust at the Source
Your security foundation is poured by your supplier. Your sourcing criteria must be ruthless and evidence-based.
Selecting a "Zero-Trust Ready" Refurbisher:
- Transparent Chain-of-Custody: Demand a digital ledger of every entity that possessed the device, from decommissioning to your dock.
- Certified Sanitization Evidence: Insist on proof of NIST 800-88 Rev. 1 "Purge"-level data destruction for all storage media.
- Component-Level Integrity Checks: Partners must have processes to detect and reject non-OEM or altered parts.
The Non-Negotiable: Hardware Bill of Materials (HBOM) Verification
By 2026, verifying the cryptographic hash of critical components (SoC, baseband processor) against OEM specifications will be mandatory. This HBOM check is your primary defense against hardware backdoors inserted deep within the supply chain.
Contractual Armor:
Your 2026 Master Service Agreements must include:
- Unannounced Audit Rights: For their sanitization facilities and repair labs.
- Software Bill of Materials (SBOM) Provision: For all firmware and pre-loaded software.
- Liquidated Damages for Security Failures: Clear financial and liability terms for post-procurement security discoveries.
Pillar 2: The Pre-Deployment "Zero-Trust Imaging" Pipeline
Every arriving device is considered hostile until proven otherwise in your controlled environment.
Step 1: Hardware-Level Diagnostics & Atomic Sanitization
Before any OS load, use dedicated tools to perform a hardware-level purge of all persistent storage (NAND, UFS). Conduct physical and electrical inspections of ports and sensors for tampering.
Step 2: Flashing the Immutable, Golden Image
This is the core of your trust. Flash a cryptographically signed, corporate-owned firmware/OS image. This "golden image," signed by your security team, overwrites any existing firmware, establishing a hardware-rooted chain of trust. It is the only acceptable starting state.
Step 3: The "Authenticate-Before-Connect" Bootstrap
The device’s first boot must connect solely to an isolated, secure provisioning service within your Zero-Trust framework. It must authenticate its hardware identity (via TPM/HSM) and pass an initial posture check before receiving policies or accessing any network resource—access is earned, never given.
Pillar 3: Identity-Centric Management & Continuous Verification
In Zero-Trust, the device is an identity, not a perimeter.
Device as a Managed Identity:
Each phone is a unique, managed identity (IMEI + hardware security key) in your Identity and Access Management (IAM) system. It must authenticate strongly for every session and resource request.
Enforce Dynamic, Micro-Segmented Policies:
Access is granular. A refurbished phone in the warehouse can access inventory systems; it cannot access R&D file shares. Policies dynamically adjust based on real-time context: user role, device health score, network location, and threat intelligence feeds.
Continuous Posture Assessment & Automated Response:
Trust is ephemeral. Implement real-time, ongoing checks:
- Has the bootloader been unlocked?
- Is the signed OS image intact (measured boot)?
- Are critical security patches applied?
A deviation triggers automated responses: step-up authentication, network segmentation, or immediate quarantine.
The 2026 End-of-Lifecycle: Closing the Zero-Trust Loop
A true protocol governs the device from cradle-to-grave-to-cradle, enabling a secure Circular Economy.
Automated, Secure Decommissioning:
Upon offboarding, automated workflows:
- Instantly revoke the device identity from all IAM and MDM systems.
- Issue a remote, hardware-level sanitization command via MDM.
Certified Data Destruction for Circularity:
Post-wipe, obtain a digitally-signed ITAD certificate of data destruction. This auditable proof allows safe return of the asset to your partner for resale, closing the loop with verifiable security.
The Immutable Digital Ledger:
Maintain a cryptographically verifiable audit trail of the entire device lifecycle: provenance, all tests, user assignments, security events, and final sanitization. This is non-negotiable for 2026 regulatory compliance (GDPR, CCPA, etc.) and forensic readiness.
Conclusion: From Liability to Strategic Advantage
This three-pillar protocol doesn't just mitigate risk; it reframes refurbished devices as a strategic lever. You achieve verified hardware security, demonstrable regulatory compliance, genuine sustainability, and significant cost optimization.
The 2026 Bottom Line: This is the blueprint for future-proof procurement. It aligns security with sustainability, turning a perceived weak link into a hallmark of a resilient, modern enterprise.
Your Next Steps for 2026:
- Conduct a Gap Analysis: Audit your current MDM, procurement, and ITAD processes against this protocol.
- Forge Strategic Partnerships: Vet and partner only with refurbishers who can meet these technical and transparency standards.
- Launch a Pilot: Implement this Zero-Trust pipeline with your next procurement cycle of refurbished phones.
The choice for 2026 is clear: govern your refurbished fleet with Zero-Trust rigor, or accept it as your greatest uncontrolled risk. Build the foundation now.
Target Keywords Integration: This protocol is built on a Zero-Trust Architecture for Corporate Refurbished Phones, managed through rigorous Mobile Device Management (MDM) and Device Posture Assessment. It secures the Supply Chain from source to IT Asset Disposition (ITAD), enabling a secure Circular Economy essential for 2026 Tech Trends.



